Legacy NAC is Infrastructure-Heavy
- VLANs and switches required
- Difficult to scale to branches
- Costly hardware & maintenance
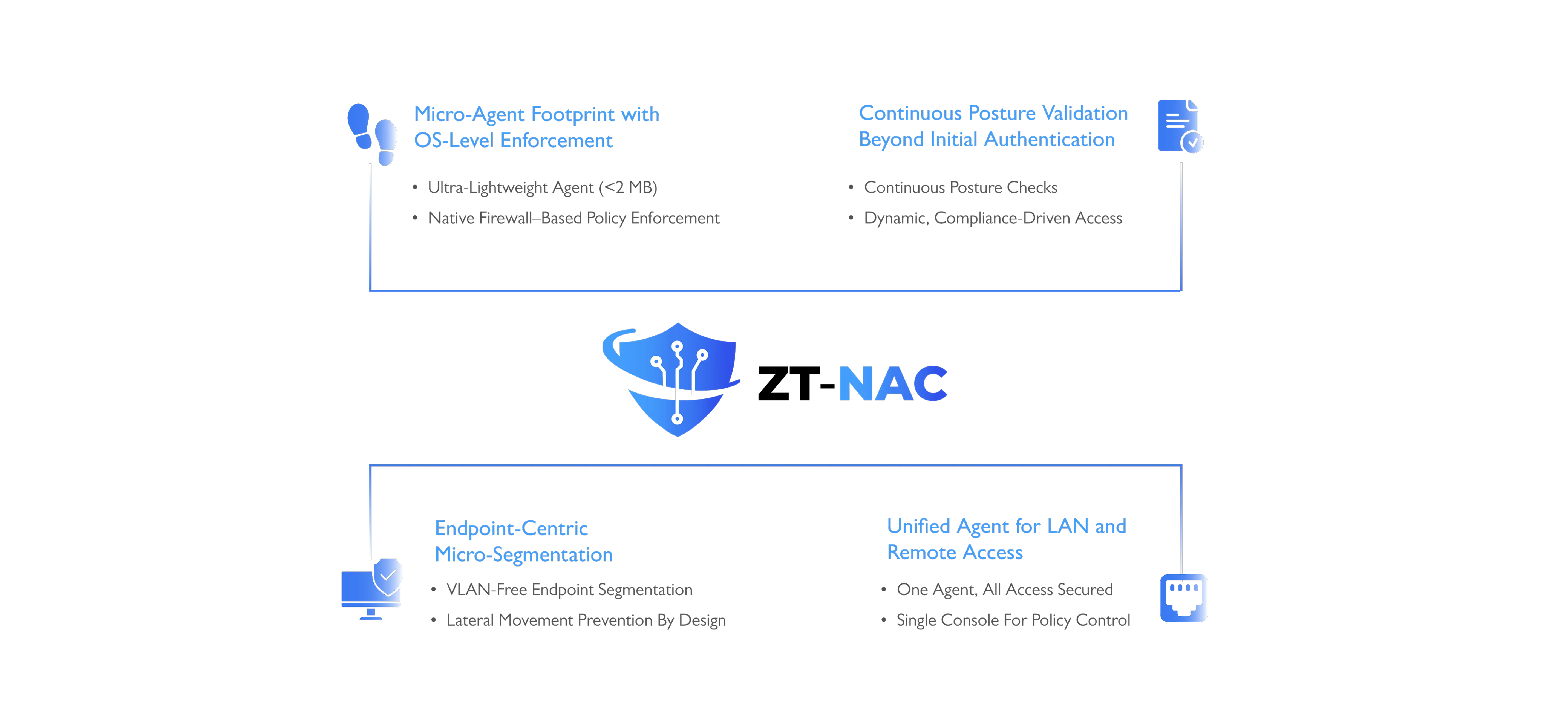
An agent-based Zero Trust NAC that enforces
access policies at the moment of connection.

COSGrid’s Zero Trust NAC is a modern, agent-based network access control solution designed to enforce strict access policies the moment a device connects to your LAN without requiring legacy VLAN segmentation or manual switch configurations.

Uses native firewall rules — no tunnels needed.
Grants access based on user, not just device.
Applies consistent policies on-prem and remote.
Validates patch, AV, encryption, and compliance instantly.
Allows scoped LAN access based on identity and context.
Enforces rules without switches or VLAN changes.
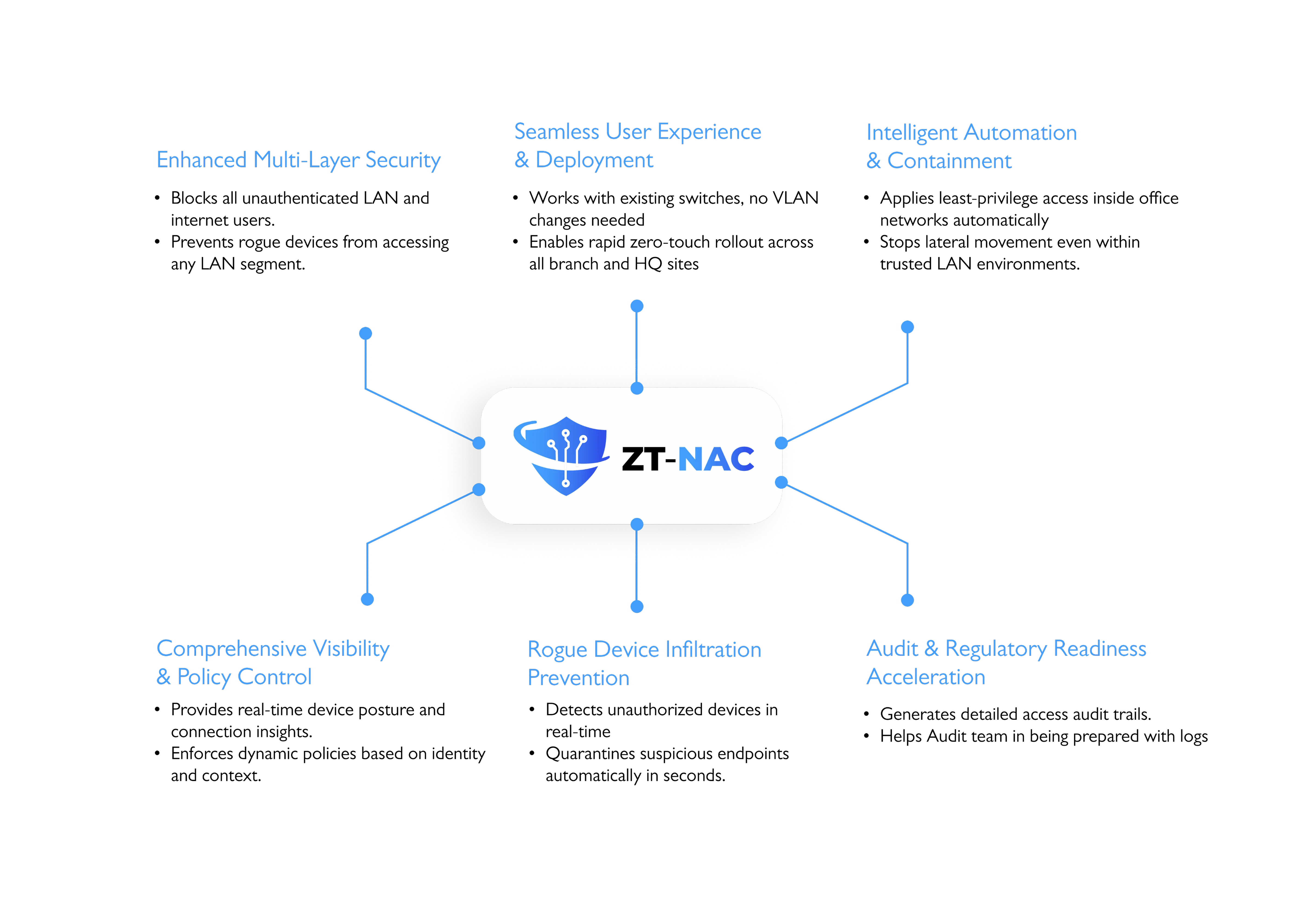
Validates every device at connection. Applies deny-by-default firewall policies
Continuously monitors patch and antivirus. Automates remediation for non-compliant devices

Profiles and segments unmanaged devices. Enforces contextual access rules automatically.

Creates temporary micro-segments for guests. Restricts guest-to-corporate network communications.

Detects unauthorized devices in real-time Quarantines suspicious endpoints automatically in seconds
Necessary Cookies
Performance Cookies
Targetting Cookies
Functional Cookies