The Kill Chain Did Not Disappear. It Accelerated.
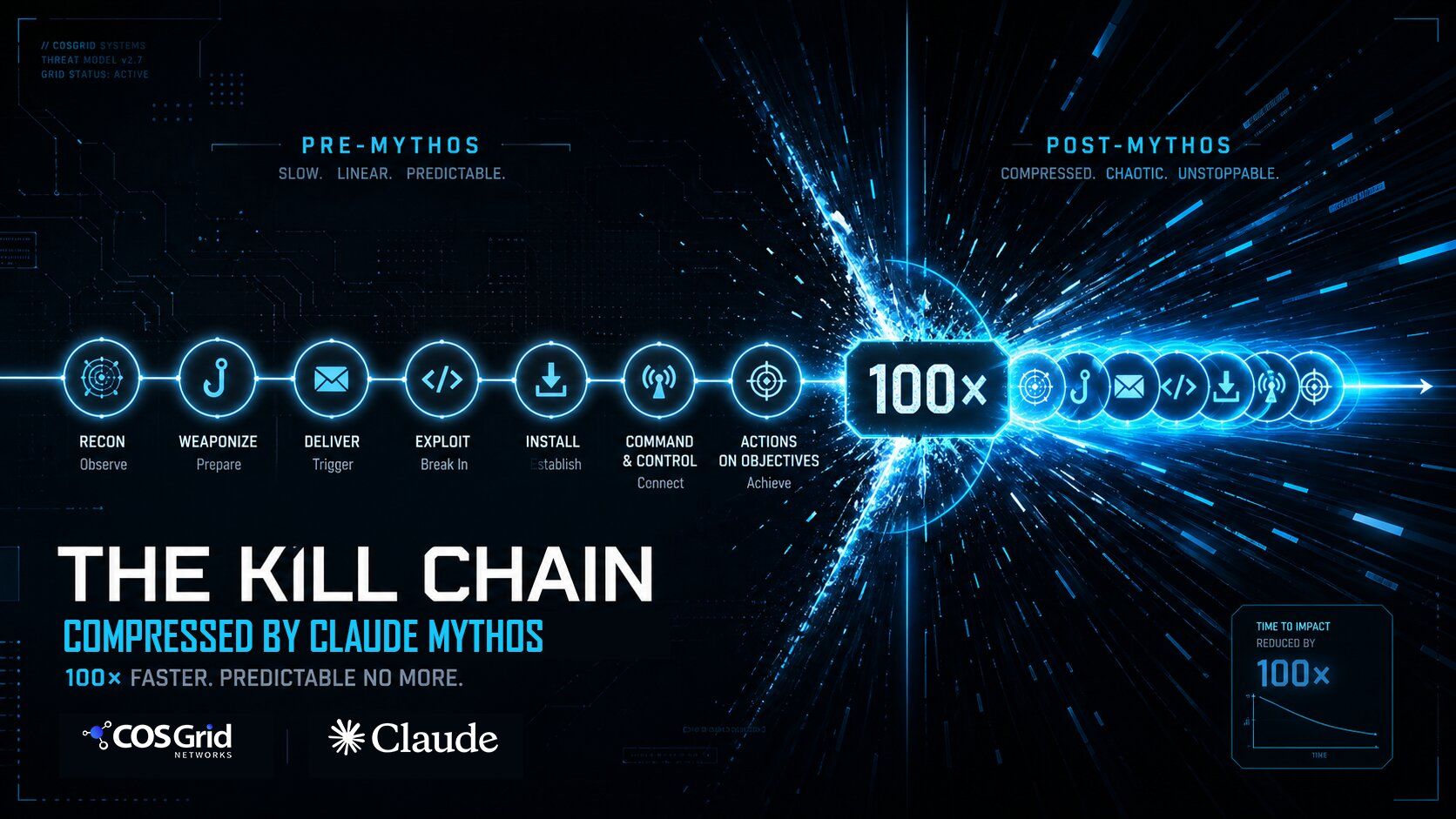
The Kill
Chain Did Not Disappear. It Accelerated.
(How AI Is Rewriting Cyberattack Economics
)
|
EXECUTIVE
SUMMARY Artificial
intelligence has not changed the objectives of cyber attackers. It has
collapsed the timeline between each phase of the kill chain from weeks and
months to hours and minutes. This blog examines the before-and-after shift in
attacker economics, maps each phase of the kill chain in the Post-Mythos era, and provides concrete defensive actions
security teams must take today. |
1. A Paradigm Shift Nobody Announced
There was no single moment when cybersecurity changed. No
press conference. No zero-day that made headlines and forced everyone to
re-architect their defenses. The shift arrived
quietly, embedded in the same AI tools organizations were enthusiastically
adopting for productivity.
The result: the cyber kill chain — the structured sequence
that attackers use to move from reconnaissance to data exfiltration — is still
intact. The phases are identical. What changed is the economics of executing
each one.
Before the AI era (what we call the Pre-Mythos
era), a sophisticated attacker needed 30 to 90 days to complete a full kill
chain. Manual reconnaissance, generic phishing kits, waiting weeks for CVEs to
be published, human-paced lateral movement — all of it added up to a timeline
that gave defenders room to detect, investigate, and respond.
In the Post-Mythos era,
that same kill chain can complete in 6 to 12 hours. AI provides attackers with
approximately 100x time compression and 50x greater adversary volume.
Signature-based defenses — built for a world where
attacks unfolded over days and weeks — are structurally unable to respond at
this speed.
2. The Kill Chain: Phase-by-Phase Comparison
The table below maps each kill chain phase against the
Pre-Mythos and Post-Mythos timelines. The transformation is not incremental —
it is a categorical change in the threat model.
|
Phase |
Pre-Mythos
Era |
Post-Mythos
Era |
|
Recon |
Manual OSINT, port scans (2–4 weeks) |
Parallel
GitHub, CT, dumps (Minutes) |
|
Initial
Access |
Generic phishing kits (Days–weeks) |
Hyper-personalized,
voice-cloned (Hours) |
|
Discovery |
Wait for published CVEs (Weeks–months) |
Autonomous
zero-day discovery (Hours) |
|
Weaponize |
One vuln, one exploit
(Days–weeks) |
Chained,
polymorphic variants (Minutes–hours) |
|
Pivot |
SMB / RDP scanning (Days–weeks) |
OAuth,
NHI, service accounts (Minutes) |
|
Persist |
Registry, scheduled tasks (Hours) |
IAM
trust, IaC state poison (Minutes) |
|
Evade |
Known TTPs, MITRE-mapped (Static playbook) |
Adapts
to your stack live (Real-time) |
|
Exfiltrate |
Human-paced data theft (Days) |
Through
legit SaaS / DNS (Minutes) |
Full kill chain duration: 30–90 days (Pre-Mythos)
→ 6–12 hours (Post-Mythos). ~100x time compression.
~50x adversary volume.
3. Deep Dive: What Each Phase Looks Like Now
· Recon:
From Patient to Instantaneous
o
In the Pre-Mythos era,
reconnaissance was a slow, methodical process. Attackers performed manual
OSINT, ran port scans, and spent two to four weeks building a picture of the
target's external attack surface. Today, AI tools can run parallel queries
across GitHub repositories, certificate transparency logs, data dumps, and API
documentation in minutes — and correlate findings into a prioritized attack
surface map automatically.
· Fingerprinting:
AI Reads Your Stack
o
Where tool-driven stack discovery once required
human interpretation, AI now correlates HTTP headers, JavaScript dependencies,
API endpoints, and identity provider signals to fingerprint an organization's
full technology stack. What once took an experienced attacker days now takes an
AI model seconds.
· Vulnerability
Discovery: Zero-Days on Demand
o
The most alarming transformation is in
vulnerability discovery. In the Pre-Mythos era,
attackers waited for CVEs to be published, then raced defenders to patch. In
the Post-Mythos era, AI can autonomously generate
exploit hypotheses and discover zero-day vulnerabilities faster than most
organizations can patch known ones. The CVE backlog is irrelevant when the
attacker does not need it.
· Initial
Access: Hyper-Personalization at Scale
o
Generic phishing kits and known social
engineering scripts have been replaced by AI-generated, hyper-personalized
lures — voice-cloned audio messages, deep-faked video calls, emails that
reference real internal context scraped from LinkedIn and GitHub. The
personalization that once required a nation-state budget is now accessible to
any threat actor with access to a large language model.
· Lateral
Movement: From Network Scanning to Identity Traversal
o
Traditional lateral movement relied on SMB and
RDP scanning — techniques that generate detectable network noise. Post-Mythos
attackers pivot through OAuth tokens, non-human identities (NHIs), and service
accounts. The blast radius of a single compromised identity now spans cloud
applications, CI/CD pipelines, IAM roles, and storage systems — all without
generating the traffic patterns that legacy tools watch for.
· Persistence:
Low-Noise, Long-Term
o
Conventional backdoors and registry
modifications have been replaced by low-noise persistence mechanisms:
long-lived OAuth tokens, misconfigured service accounts, and shadow
applications that quietly exfiltrate data through legitimate API channels.
These persist across password resets and MFA reconfigurations — and are often
invisible to endpoint detection tools.
· Exfiltration:
Hidden in Plain Sight
o
Where batch data theft once left detectable
anomalies in network egress logs, modern exfiltration flows through legitimate
SaaS export functions, DNS channels, and OAuth-authorized third-party
applications. The data leaves through the front door, indistinguishable from
authorized business operations.
4. Why This Breaks Signature-Based Defense
The security industry spent two decades building defenses optimized for a world where attacks were slow,
signatures were stable, and TTPs were predictable enough to map to frameworks
like MITRE ATT&CK. That model assumed defenders had time — time to detect,
time to investigate, time to respond.
AI-accelerated attacks eliminate that assumption. Consider
the implications:
• A SIEM rule written for a known
TTP is obsolete the moment the attacker's AI adapts its approach to the
target's specific stack
• Threat intelligence feeds that
operate on 24-hour cycles cannot provide actionable signal for attacks that
complete in 6 hours
• Human analysts cannot triage at
the speed required when attackers chain five kill-chain phases in the time it
takes to open a ticket
• Patch management cycles
measured in weeks are irrelevant when zero-day discovery and weaponization
happen in hours
The architecture of defense must
shift from reactive detection to proactive prevention — from signature matching
to behavioral anomaly detection, from periodic
patching to continuous exposure management.
5. What Defenders Must Do: Five Structural Priorities
Priority 1: Continuous API and Shadow Asset Discovery
You cannot protect what you cannot see. The Post-Mythos attacker's recon phase maps your external attack
surface faster than your asset inventory is updated. Defenders must implement
continuous, automated discovery of APIs, shadow applications, and non-human
identities — not quarterly audits, but real-time visibility.
• Deploy API discovery tools that
enumerate all active endpoints, including undocumented and shadow APIs
• Inventory all service accounts,
OAuth grants, and non-human identities across cloud tenants
• Map third-party integrations
and their data access scopes
Priority 2: Identity Hardening
Identity is the new perimeter. When attackers pivot through
OAuth tokens and service accounts rather than network protocols, hardening
identity becomes the single highest-leverage defensive investment.
• Enforce least-privilege across
all IAM roles and service accounts
• Implement continuous monitoring
of OAuth grant scopes and revoke unnecessary permissions
• Harden SSO configurations and
enforce phishing-resistant MFA
• Establish clear tenant
boundaries and cross-tenant access controls
Priority 3: Schema Validation and Positive Security
Controls
Negative security models (block what is known bad) fail
against novel AI-generated attacks. Positive security controls (allow only what
is explicitly permitted) are structurally more resilient.
• Implement API schema validation
to enforce expected request structure and reject anomalies
• Define positive security
policies for all external-facing APIs
• Use Web Application and API
Protection (WAAP) platforms that enforce behavioral
baselines
Priority 4: Behavioral Anomaly
Detection
When exfiltration looks like a normal export and persistence
looks like a legitimate service account, signature detection is blind.
Defenders must build behavioral baselines and detect
deviations — not known signatures.
• Monitor for abnormal data
export volumes, even through legitimate SaaS channels
• Detect token abuse patterns:
unusual access times, geographic anomalies, scope escalation
• Correlate low-noise signals
across application, IAM, CI/CD, and storage layers
Priority 5: Rapid Virtual Patching
When zero-day discovery compresses to hours, patch
management cycles measured in weeks are a liability. Virtual patching —
applying protective controls at the perimeter without modifying the underlying
application — closes the gap between vulnerability discovery and permanent
remediation.
• Deploy virtual patching
capabilities that can be applied in minutes, not days
• Integrate threat intelligence
with automated rule deployment pipelines
• Measure and minimize mean time
to protection (MTTP) as a primary security KPI
6. The COSGrid Perspective
At COSGrid Networks, we designed
our platform around the recognition that the kill chain did not disappear — it
accelerated. Our approach to cloud-native security is built on four pillars
that directly address the Post-Mythos threat model:
• Continuous API discovery and
runtime protection to eliminate shadow attack surface
• Identity-aware access controls
that enforce least privilege across cloud and SaaS environments
• Schema-based positive security
enforcement that is resilient to novel attack patterns
• Real-time behavioral
analytics that detect low-noise persistence and anomalous data flows