Despite MFA and compliance measures, Attacks are inevitable

Excellence is a moving target, they say! If there is one domain that's so dynamic that one needs to continuously keep up in the game, it's none other than cybersecurity. While organizations are better at cyber security these days, the kind of sophisticated attacks fueled by AI & ML capabilities render the defendending organization on a backfoot, even though they adopt best practices including MFA & basic SOC2 and ISO 27000 Compliance.

Ensuring compliance, however, it does not assure a Cyber-safe system. Even with the implementation of Multi-Factor Authentication (MFA) and other security measures, attacks cannot be completely avoided. CXOs need to acknowledge that while compliance frameworks are necessary for regulatory compliance, genuine security necessitates a proactive and comprehensive approach to detecting and mitigating threats.
While Identity remains a key protection pillar enabled by MFA, numerous MFA bypass attacks showcase that organizations cannot go complacent having implemented MFA. However, even this approach may not guarantee foolproof protection. The emergence of MFA fatigue, Man-in-the-middle attacks, and Token theft necessitates the adoption of a Zero Trust approach to cybersecurity.
Ensuring cybersecurity goes beyond safeguarding sensitive data; it is crucial for maintaining the overall operational integrity and reputation of your business. Any security breach could lead to financial setbacks, legal consequences, and a loss of trust from both clients and stakeholders. Given the rising complexity of cyber threats, having strong cybersecurity protocols is no longer a choice but a must. By giving importance to cybersecurity, companies can reduce risks, adhere to regulations, and create a safe space for business activities.
By incorporating MFA, organizations can significantly mitigate the risk of unauthorized access, even if one factor is compromised. However, further exploration of this subject will reveal why relying solely on MFA may not be completely secure in safeguarding your business against cyber threats.
While Multi-Factor Authentication (MFA) is a robust security measure, it's not without its limitations. Hackers have devised sophisticated methods to bypass MFA controls, including social engineering attacks or SIM swapping. Moreover, some applications or systems may not fully support MFA, leaving potential vulnerabilities. Understanding these limitations is crucial for businesses aiming to fortify their defenses.
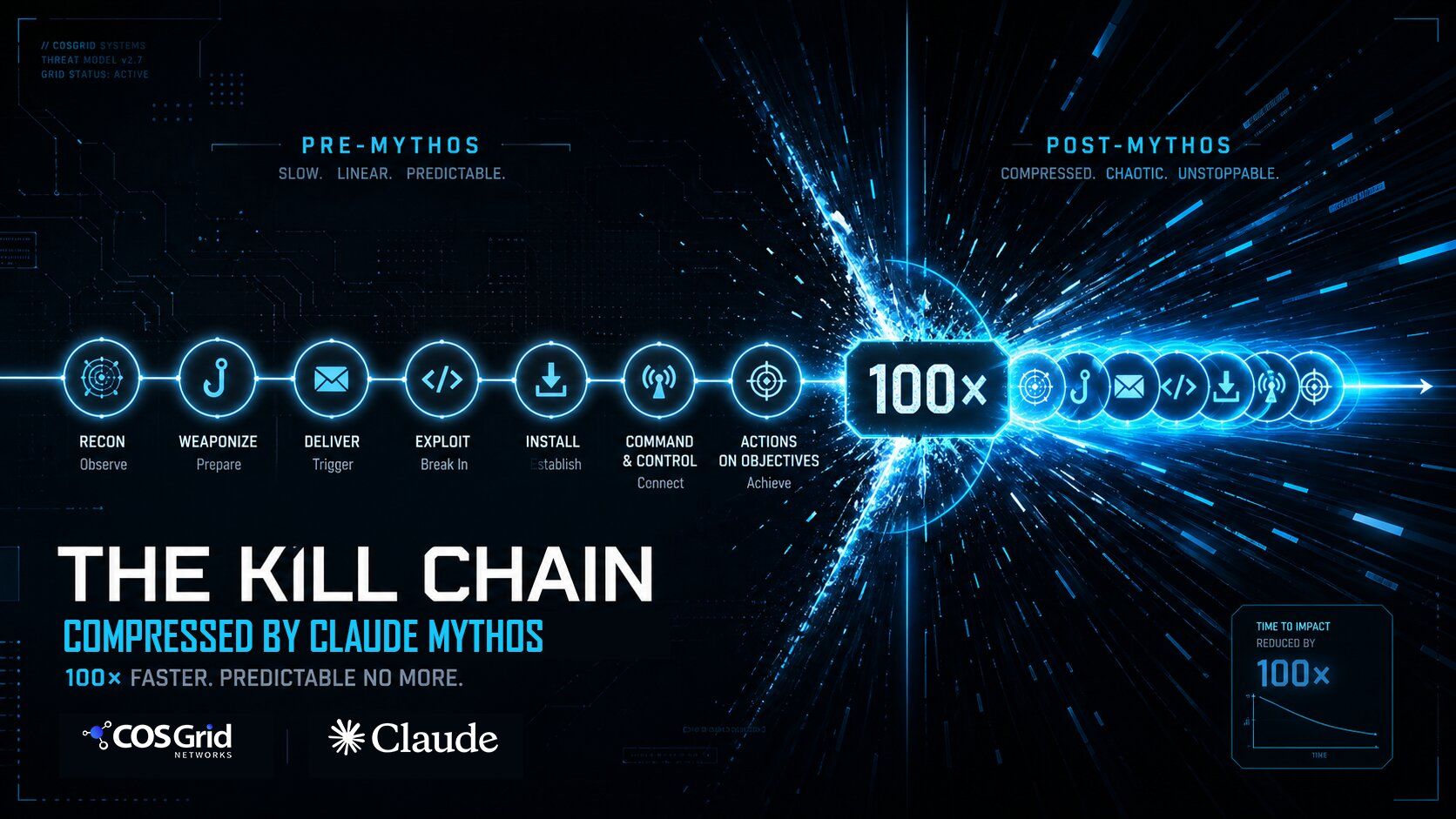
MFA Bypass attacks
MFA fatigue
Attackers use stolen credentials to repeatedly try logging into targeted accounts, overwhelming users with verification requests. For those organizations where users have push or SMS notifications enabled as part of their MFA protection, the targeted users are bombarded with login verification requests. Users, frustrated or by accident, may end up clicking a malicious link, providing the threat actor with unauthorized access.

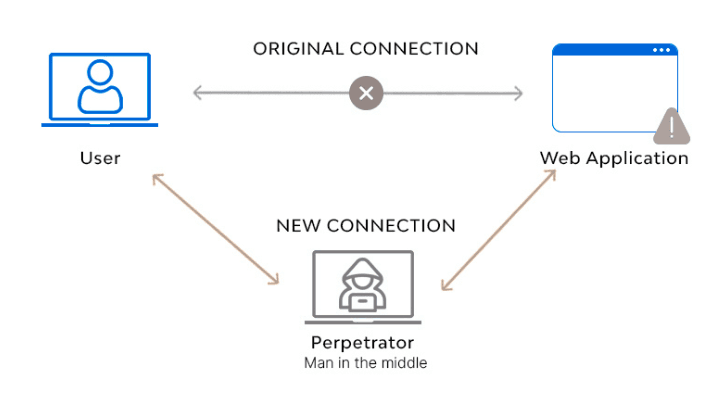
Man-in-the-middle
Also called, In session hijacking or real-time phishing, attackers trick users into giving username/password. Now, with MFA, attackers need both credentials and a second authentication form. They insert themselves between user and login page. Victims receive requests from MFA providers, leading to a fake login page. Attackers capture credentials, modify session cookies, and gain immediate access to target systems. More attack variations expected.
Token theft
To prevent users from having to log in again and again, "session cookies" are saved on their devices. Unfortunately, these cookies can be stolen by malicious individuals. The stolen session cookies are then used by the attacker to deceive the browser into thinking that the legitimate user is being authenticated. Once inside, the attacker gains access to all the privileges and actions that the trusted user had with that particular cookie

Password Reset -Identity Attack - Variant of Token Theft
MFA bypass attack on MGM, Caesars
Attackers are harvesting information about privileged users from LinkedIn and using vishing attacks on corporate IT help desks to reset MFA devices and SIM swaps. They exploit features in Identity & Access Management (IAM) for more control and exfiltrate customer data using Ransomware as a Service (RaaS) to encrypt and lock businesses. The below is the high level events that led to the cyberattacks at MGM.
-
Analyze / Reconnaissance: Harvest info about a privileged User (Victim) from LinkedIn
-
Entry and take a Position / Weaponization:: Vishing attack on corporate IT helpdesk, seek MFA device reset, SIM swapping, etc.
-
Privilege Escalation:: Exploit features in Okta (inbound federation) for more control
-
Exploitation:: Synchronization of credentials between on-prem and cloud resources
-
Action: Exfiltration of customer data and use of Ransomware as a Service (RaaS) to encrypt & lock for the business
Caesars reportedly paid $15 million in ransomware, while MGM suffered heavily for ten days.

In addition to Multi-Factor Authentication (MFA), businesses should explore implementing measures such as zero Trust, intrusion detection systems, regular security audits, employee cybersecurity training, encryption protocols, and network segmentation. It's essential to adopt a multi-layered approach to cybersecurity to mitigate risks effectively.
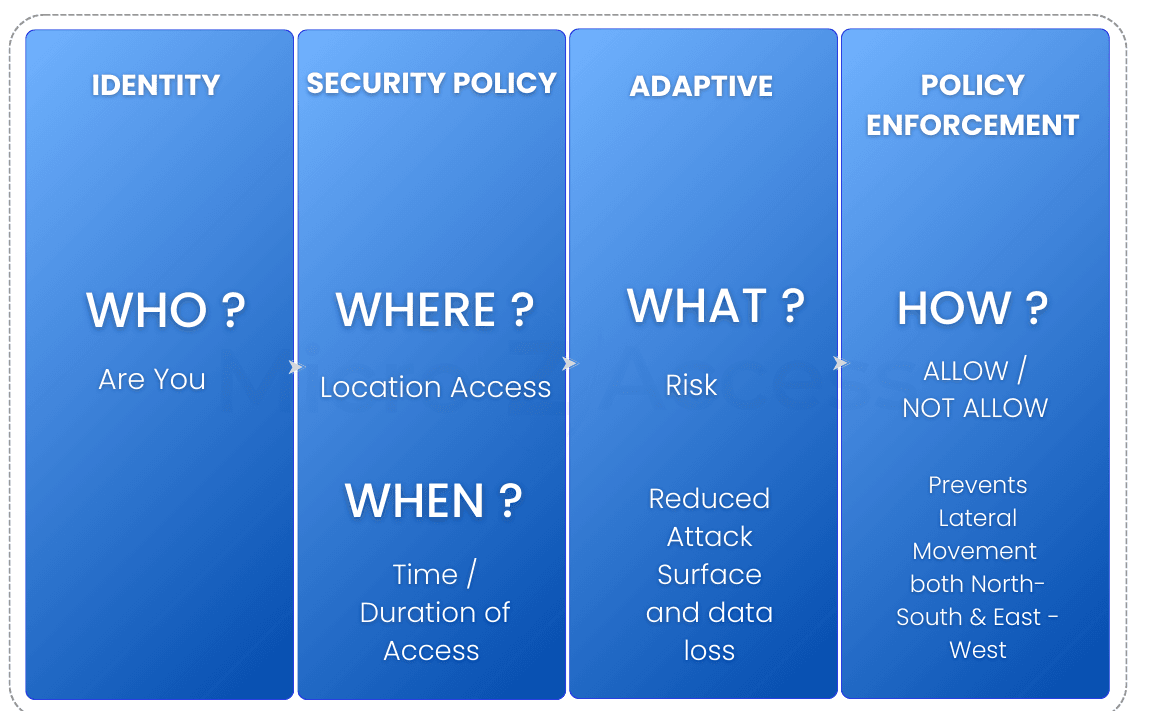
For fool proof cyber security, organizations need to adopt a first principles approach for a truly formidable protection of assets. This includes 5 Ws: What, Why, When, Who, How
Way Forward
With this approach, Zero trust architecture was formulated and the framework outlined by NIST 800-207 provides a comprehensive approach. Even MFA and Complaince, the addition of Zero Trust will enhance your security posture much superior. Again, instead of adopting Zero trust products, deploy the one that suits the use case.