Five Aspects of Zero Trust Network Access (ZTNA) that Business VPN users might be unaware
_4ca37943-da33-4e29-ae43-a68297485d02.png)
In today's technology landscape, complexity has increased significantly, making it more challenging to navigate and achieve desired outcomes. A commitment to ongoing learning and unlearning is imperative, particularly in the ever-evolving field of Cybersecurity, which is characterized by numerous knowns and unknowns in the midst of technology jargons and new product categories.
While many businesses are familiar with the term "Zero Trust," its depth and transformative potential often remain unexplored. Have you ever felt like your Organisation VPN is more of a virtual "pain" network? Slow speeds, complex configurations, and lingering security concerns are all too common with traditional VPNs.
After extensive discussions with various IT and Security teams, as well as CIOs and CISOs across verticals and organizations of various sizes, We have compiled a few critical aspects & understanding gaps related to Zero Trust Network and use cases.
1) Zero Trust Access Makes Applications and Workloads Invisible in the Internet
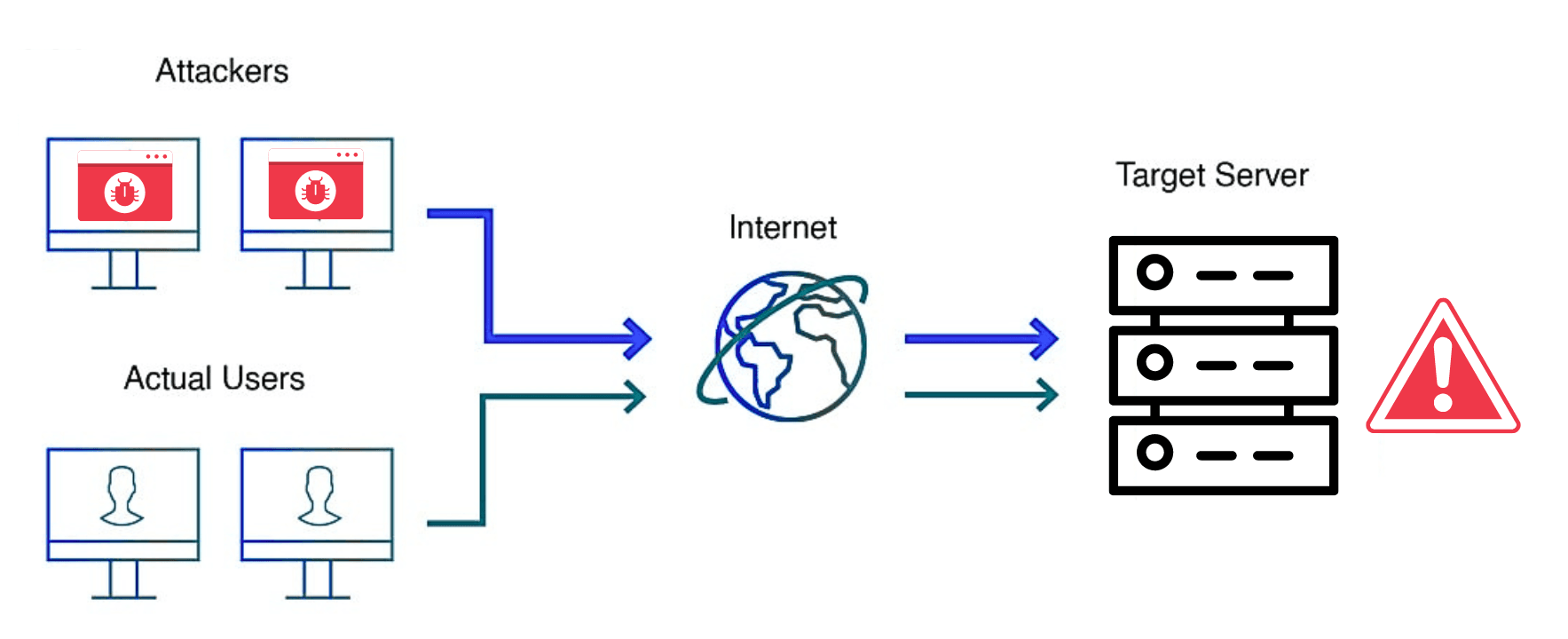
Unlike VPN, Zero Trust Network Access (ZTNA) restricts the Application Discovery on the Internet, ensuring that servers are protected from DDoS attacks, malware, and other online threats to organizations. Access is restricted solely to authorized users and the endpoint ie) asset is visible only to the authorized ones.
Server Protection:
By Implementing ZTNA, We can prevent DDoS attacks since DDoS attacks target specific IP addresses. With ZTNA's Distributed Architecture applications are not directly exposed, making it challenging for attackers to launch effective DDoS attacks.
_7c2f5475-d1e2-48d5-a0c9-f42b636eabe0.png)
Eliminating the Network Perimeter
Conventional networks depend on a defined perimeter, which exposes internal resources to external threats. Zero Trust discards this notion, considering all users and devices as potentially untrustworthy.
Direct Connections from Users to Applications
Users establish direct links to applications, circumventing the network and thereby minimizing the attack surface.
Micro-segmentation
By establishing distinct network segments, the visibility of applications and workloads to potential attackers is significantly reduced.Dynamic Access Controls
Continuous verification of the context surrounding users, devices, and applications effectively prevents unauthorized access.Note :
ZTNA protects against 22 Known Exploited Vulnerabilities (KEVs) discovered by CISA related to VPN. CISA recommends ZTNA architecture that uses a trust broker.2) Centralized Management; Automation and Orchestration
Centralized Management
Centralized console for the supervision and administration of Zero Trust policies, user identities, and device configurations throughout the entire organization.Automation
Enhances the efficiency of Zero Trust policy development, implementation, and adjustment, thereby minimizing the need for manual involvement and the potential for errorsOrchestration
Integrates various Zero Trust components and systems to guarantee smooth functionality and effective management of security incidents.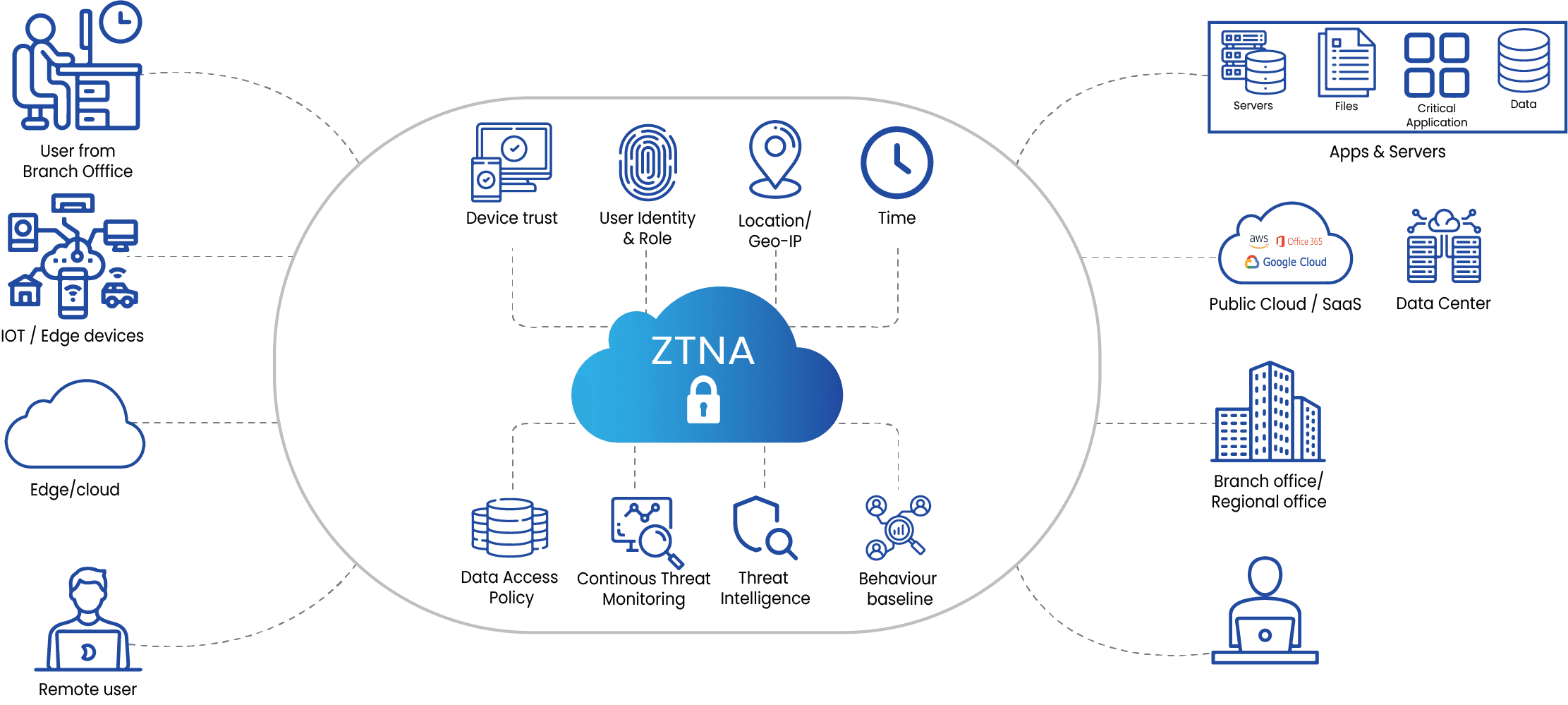
3) Zero Trust Access Can handle East - West Traffic
By segmenting workloads and implementing stringent access controls, Zero Trust effectively mitigates the lateral movement of threats, even in the event of a compromised device within the network and in Multi-cloud Workload environmentKey components of ZTNA for east-west traffic management
Micro-segmentation
Creating isolated segments for different applications and workloads.Identity and Access Management (IAM)
Enforcing strong authentication and authorization for access between micro-segments.Continuous Monitoring
Continuously monitoring network traffic for anomalies and threats.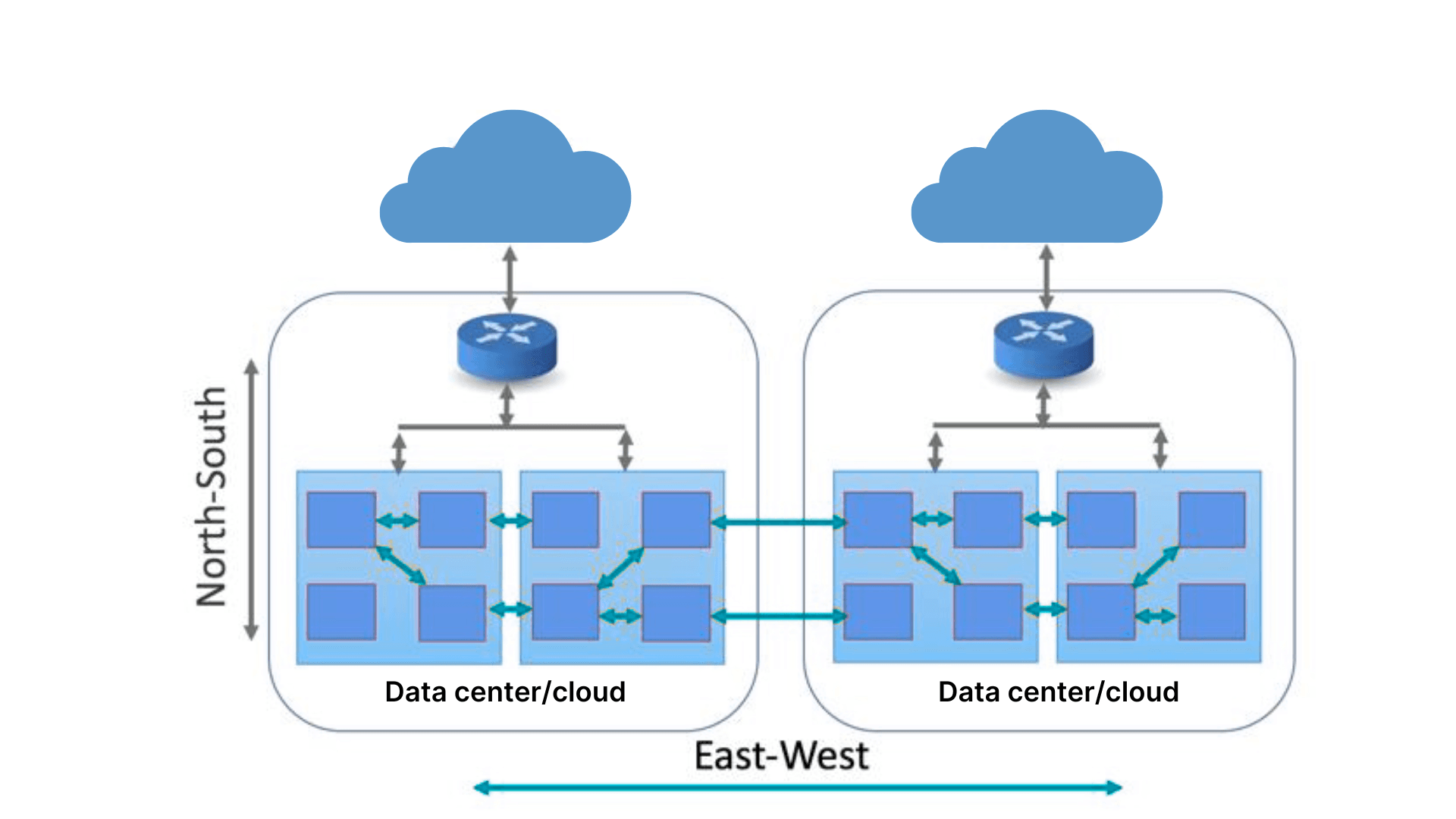
4) Zero Trust Access Combine with legacy IPSec for improved Security and effectiveness
While Zero Trust Network Access (ZTNA) offers significant advancements in network security, integrating it with legacy IPSec can provide a hybrid approach to bolster security and ensure a smooth transitionAdvantages of Integrating ZTNA and IPSec
Phased Transition
Organizations have the opportunity to gradually retire outdated VPN systems while ensuring continuous connectivity.Improved Security
ZTNA offers supplementary security measures for IPSec tunnels, safeguarding against new and evolving threats.Performance Enhancement
By directing certain traffic through IPSec, ZTNA can enhance the overall efficiency of the network.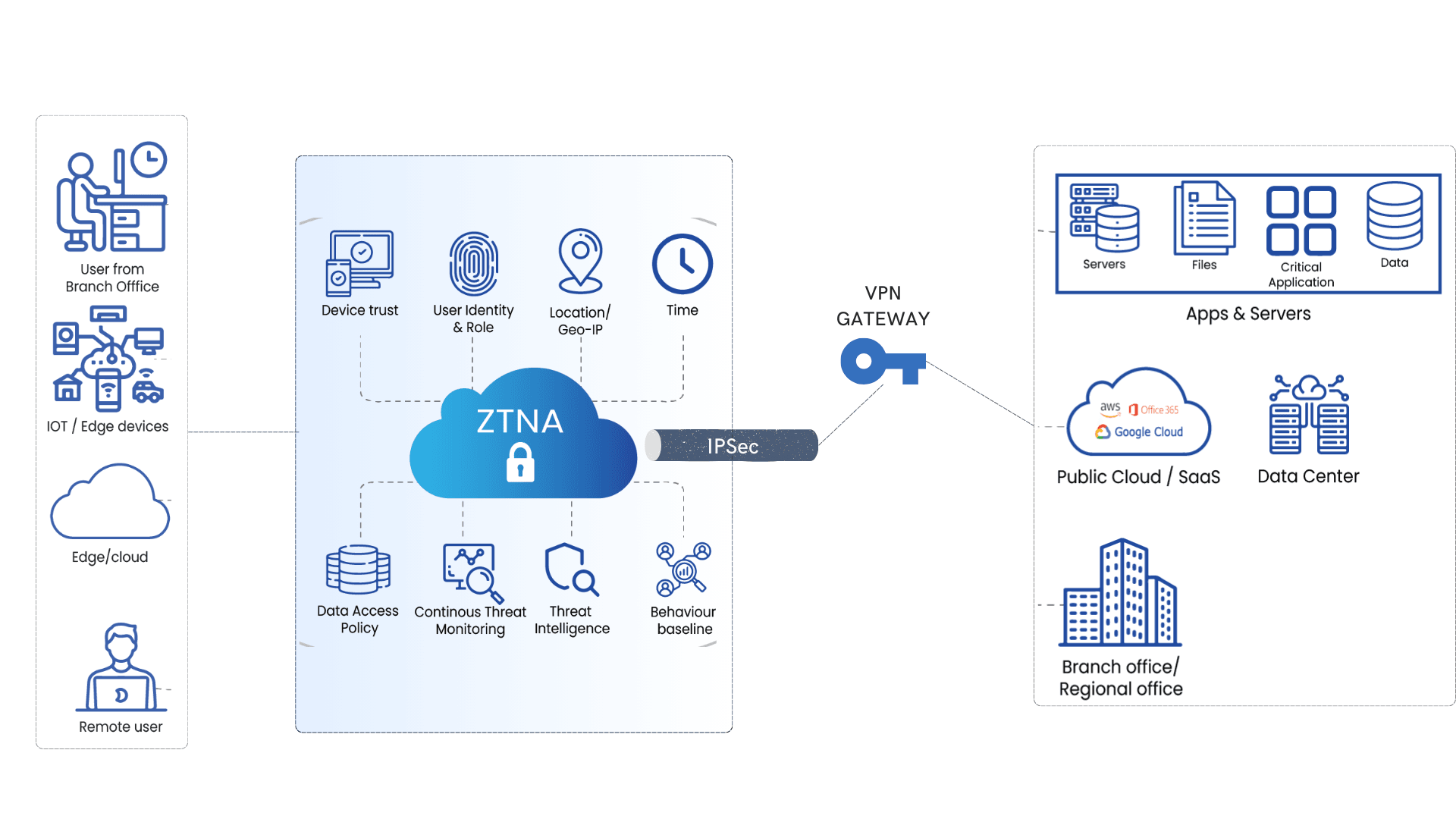
5) Compared to VPN, Zero Trust Access is Cost-effective in Overall TCO
Although VPNs may present lower initial expenses, the Hidden costs linked to security breaches, overall Infrastructure & operations expenses, bandwidth and management burdens can rapidly surpass the initial savings. ZTNA provides a more sustainable and economically viable solution for securing remote access.Lower Bandwidth Cost
Decentralized Peer to peer Mesh access and streamline traffic management can contribute to decreased bandwidth expenses.Strengthened Security
Continuous verification offered by ZTNA significantly diminish the likelihood of data breaches and reduce the attack surface risk by 90% which can result in considerable financial repercussions.Increased Productivity
Faster Access with enhanced user experience leads to increased productivity and thereby lowering IT support expenditures.Lower Hardware and Maintenance Expenses
ZTNA solutions operate in the cloud, removing the necessity for on-site hardware and the related upkeep costs.To sum up, Zero Trust Network Access (ZTNA) marks a major leap forward in the realm of network security and access control when compared to conventional VPNs. By transitioning from a network-focused approach to one that prioritizes the user, ZTNA delivers superior protection, better performance, and increased adaptability. As more organizations turn to cloud applications and support remote work, ZTNA stands out as the ideal choice for protecting sensitive information and facilitating secure collaboration.