Zero Trust NAC: Is Traditional NAC Dead in Hybrid Work?

Is Traditional NAC Dead? Why Zero Trust is the Only Path Forward in Hybrid Work
Remember when your biggest security concern was stopping unauthorized users from plugging into your office network? Those days feel like ancient history.
Network Access Control (NAC) once ruled the enterprise security landscape—a fortress-like approach that worked perfectly when everyone sat in cubicles, used company-issued laptops, and accessed resources from behind a well-defined corporate perimeter. But here's the uncomfortable truth: that world no longer exists.
Today's reality paints a starkly different picture. 28.2% of full-time employees work in hybrid models, 60% of remote-capable workers demand flexible arrangements, and your "secure perimeter" now extends to home offices, coffee shops, and co-working spaces across the globe. Your employees are accessing mission-critical applications from personal devices, over public Wi-Fi, at 2 AM in different time zones.
So the question isn't whether NAC is relevant—it’s whether traditional NAC can possibly survive in this new landscape.
The short answer? Not in its current form.
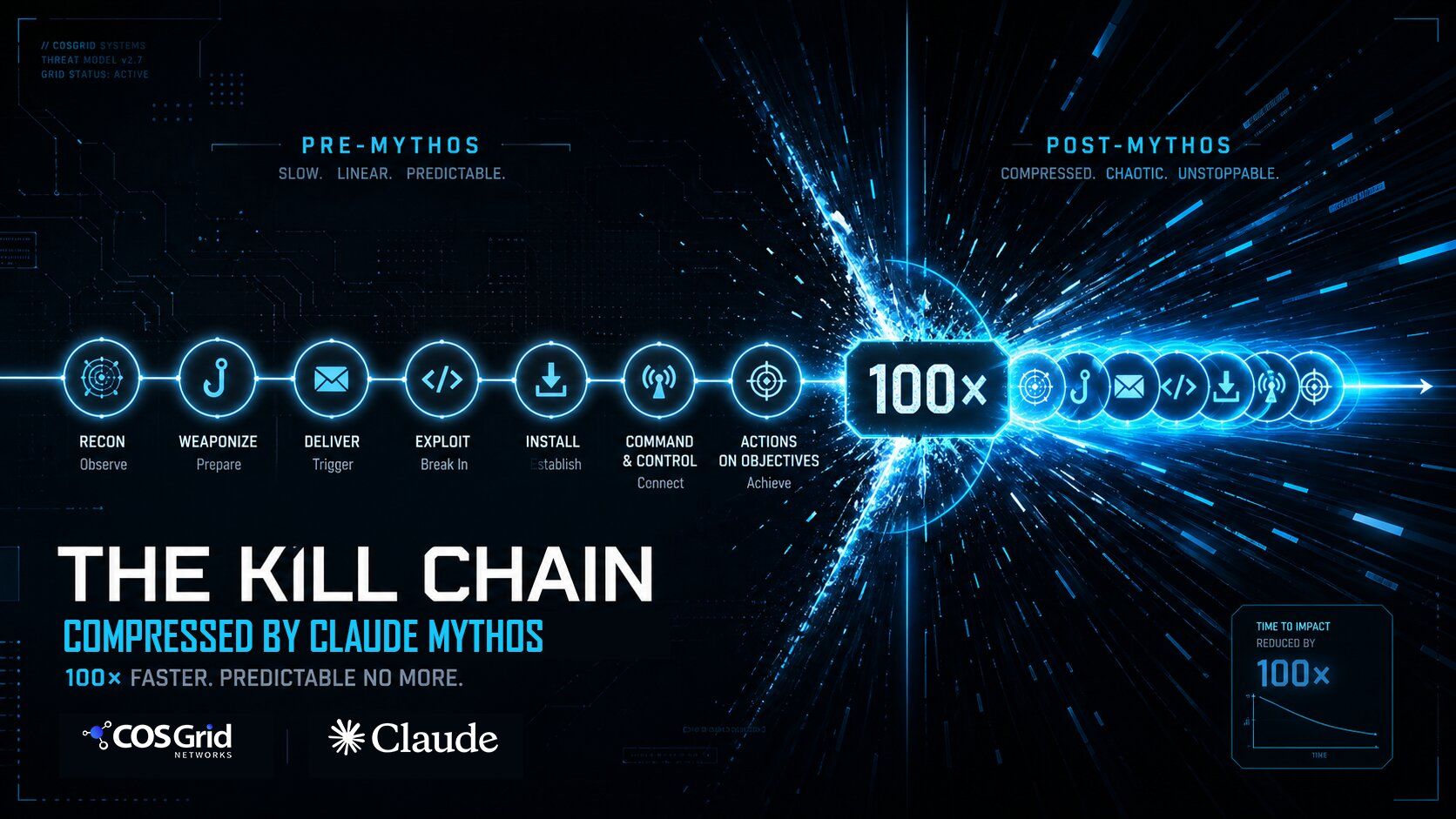
Legacy NAC solutions are buckling under the weight of modern work realities. They were designed for a world that no longer exists, built on assumptions that are now liabilities. When your security model assumes users are "inside" or "outside" the network, what happens when the network is everywhere and nowhere at once?
Industry analysts aren't sugar-coating this transformation. Gartner projects that by 2025, 60% of companies will abandon VPNs for Zero Trust solutions, while % of new remote access deployments will leverage Zero Trust Network Access (ZTNA) instead of traditional VPN services—a massive leap from less than 10% just three years ago.
The writing is on the wall: the hybrid work revolution hasn't just changed how we work—it’s fundamentally broken the security models we've relied on for decades.
But here's where the story gets interesting. While traditional NAC is dying, the core concept of network access control isn't obsolete—it’s evolving. Smart organizations aren't abandoning access control; they’re reimagining it through a Zero Trust lens that treats every user, device, and connection as potentially hostile until proven otherwise.
This isn't just about upgrading technology—it’s about surviving in a threat landscape where yesterday's security strategies become tomorrow's attack vectors.
Is your organization struggling with NAC challenges in hybrid work environments? Learn how Zero Trust NAC solutions deliver enterprise-grade security for distributed teams while reducing operational complexity.
The Critical Challenges Exposing Traditional NAC's Fatal Flaws
Gartner defines network access control (NAC) as technologies that enable organizations to implement policies for controlling access to corporate infrastructure by both user-oriented devices and Internet of Things (IoT) devices. However, legacy NAC systems, built for perimeter-based security, create critical gaps that expose organizations to sophisticated cyber threats, compliance violations, and operational inefficiencies in today's identity-driven access scenarios.
1. Infrastructure Dependency and Scalability Limitations
Traditional NAC requires extensive hardware investments including dedicated appliances, switch configurations, and VLAN segmentation. This infrastructure-heavy approach creates:
- Significant deployment costs across distributed locations
- Complex scalability challenges for growing organizations
- Ongoing maintenance overhead consuming IT resources
2. Location-Based Trust Models Creating Security Blind Spots
Legacy systems grant access based on network location rather than identity verification. Once connected to the corporate LAN, devices often receive broad network access without continuous validation, enabling:
- MAC address spoofing attacks to bypass access controls
- Lateral movement within networks after initial authentication
- Persistent compromised sessions without continuous monitoring
3. Device Security Posture Gaps in BYOD Environments
With personal devices accessing company data, organizations lose visibility into device compliance when employees work from various locations. Critical risks include:
- Outdated operating systems and missing security patches
- Disabled antivirus protection and unauthorized applications
- Insufficient real-time posture assessments on diverse endpoints
4. Static Policy Management and Operational Complexity
Traditional NAC policies are static and difficult to modify, creating:
- Extensive manual management requirements
- Increased risk of security misconfigurations
- Reduced agility in responding to evolving threats
5. Compliance and Audit Trail Deficiencies
Regulatory requirements demand comprehensive network access visibility, which legacy NAC struggles to provide through:
- Incomplete logging and reporting capabilities
- Limited real-time visibility into user activities
- Inconsistent policy enforcement between locations
How Zero Trust NAC Bridges Critical Security Gaps
COSGrid's Zero Trust Network Access Control (ZT-NAC) represents a fundamental shift from traditional perimeter-based security to an identity-centric, "never trust, always verify" approach. Built on the NIST 800-207 Zero Trust Architecture framework, COSGrid ZT-NAC addresses critical hybrid work challenges through innovative agent-based enforcement.
Identity-First Access Control Architecture
Zero Trust NAC implements "never trust, always verify" principles, granting access only after validating both user identity and device security posture. This approach delivers:
Multi-Factor Authentication Integration
Seamless integration with existing SSO and MFA systems ensures strong user authentication across all access points.
Device Identity Validation
Unique device fingerprinting prevents spoofing attacks and ensures explicit authorization for each endpoint.
Continuous Identity Verification
Regular re-authentication maintains session integrity throughout connection periods.
Real-Time Security Posture Assessment
COSGrid ZT-NAC performs continuous device posture validation including:
- Patch level verification ensuring current security updates
- Antivirus status validation confirming active protection
- Encryption compliance verification for data protection
- Application control monitoring and restriction capabilities
This comprehensive security posture assessment works consistently whether employees are in the office, at home, or any remote location, eliminating the blind spots that plague traditional NAC solutions.
Simplified Operations with Agent-Based Enforcement
COSGrid ZT-NAC eliminates infrastructure complexity through:
- Zero-Touch Deployment: Cloud-hosted controllers enable 15-minute setup across locations
- No Infrastructure Changes: Works with existing networks without VLAN modifications
- Unified Management: Single console provides complete endpoint visibility and control
Ready to see how quickly you can deploy Zero Trust security? Contact COSGrid Networks to learn about our 15-minute implementation process.
Traditional vs. Zero Trust NAC: Executive Comparison
The market shift toward Zero Trust architectures is evident in enterprise adoption patterns. Gartner identifies Zero Trust Network Access as a fast-growing market with consistent buyer trends toward integrated solutions that eliminate vendor sprawl.
| Traditional NAC | Zero Trust NAC |
|---|---|
| Network-location-based trust | User & device identity-first |
| VLAN-based enforcement | Agent-based or OS-native enforcement |
| Mostly on-premises, static | Cloud-managed, dynamic, scalable |
| 802.1X-centric authentication | Works with or without 802.1X |
| Point-in-time posture checks | Continuous real-time posture validation |
| Hardware-intensive infrastructure | Infrastructure-light, software-defined |
| Perimeter security mindset | Zero Trust "never trust, always verify" |
Industry Use Cases and ROI Impact
Financial Services
Banks implementing COSGrid ZT-NAC achieve 90% reduction in lateral threat movement while maintaining regulatory compliance across distributed branch networks.
Healthcare Organizations
Medical facilities secure BYOD environments and IoT devices while ensuring HIPAA compliance through COSGrid's continuous posture assessment and identity verification.
Manufacturing Companies
Industrial organizations protect OT networks and remote facilities through COSGrid's agent-based segmentation without disrupting operational technology systems.
Technology Companies
Software firms enable secure remote development environments while protecting intellectual property through COSGrid's dynamic access control and real-time monitoring.
Quantifiable Business Benefits
Organizations implementing COSGrid ZT-NAC typically experience:
- 90% reduction in lateral threat movement through endpoint-level segmentation
- 60% cost savings compared to traditional solutions by eliminating hardware appliances
- 3x faster incident containment through real-time visibility and automated response
- 15-minute setup for new locations, dramatically reducing deployment timelines
Want to calculate your potential ROI? Schedule a consultation with COSGrid Networks to assess your specific cost savings and security improvements.
Strategic Implementation Considerations
Future-Proofing Network Security
COSGrid ZT-NAC provides organizational resilience through:
- Scalable Architecture: Cloud-based management scales naturally with organizational growth without infrastructure limitations.
- Technology Agnostic Design: Compatible with diverse device types, operating systems, and network infrastructures while maintaining consistent security standards.
- Continuous Innovation: Regular updates ensure COSGrid's solution evolves with emerging security threats and business requirements.
Executive Decision Framework
When evaluating Zero Trust NAC solutions, consider Gartner's emphasis on:
- Security Service Edge (SSE) strategy integration capabilities
- Agent-based deployment models for simplified management
- Unified platforms that reduce vendor sprawl and operational complexity
- Solutions that address both traditional NAC and modern ZTNA requirements
- Integration capabilities with existing security infrastructure
- Scalability across distributed locations and remote workers
- Compliance reporting and audit trail comprehensiveness
- Total cost of ownership including operational efficiency gains
Conclusion: The Imperative for Zero Trust Network Security
Traditional NAC solutions cannot address the identity-driven, location-agnostic security requirements of modern hybrid work environments. The question for organizational leaders is not whether to adopt Zero Trust Network Access Control, but how quickly implementation can begin to protect distributed workforces and critical business assets.
COSGrid ZT-NAC delivers immediate security benefits while providing the foundation for future organizational growth and competitive advantage in an increasingly distributed business landscape.
Ready to transform your network security for the hybrid work era?
Contact COSGrid Networks today to learn how ZT-NAC can eliminate your current NAC challenges while providing the robust security foundation your organization needs for sustainable growth and success.
Transform your hybrid work security posture in just 15 minutes. Reach out to COSGrid Networks to begin your Zero Trust journey.